In this post, how to configure a Site2Site VPN connecting using a Checkpoint firewall.
[EDIT: The instructions below are for R77, which is a really old version. I’m currently writing the instructions for the R80.20 version, but it seems it’s a bit harder to get the S2S tunnel up and stable.. certainly on my PPPOE internet connection… more updates soon!
But in case you still want to make this work, please check this hidden article with my notes.. that have not been validated yet! [/EDIT]
While http://msdn.microsoft.com/en-us/library/azure/dn133795.aspx tells you how to create the Site2Site VPN, the firewall part only covers Juniper or Cisco appliances. As I do not own such a device, I got to work on the Checkpoint together with Syed Pasha.
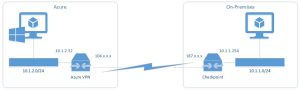
Below the network overview…
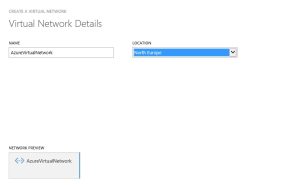
So the start is to create a network inside Windows Azure. This network will be used to connect our VM’s and services too. The previously mentioned link
Click Create a virtual network and follow the wizard, give the network a name and in which location you want it to be created:
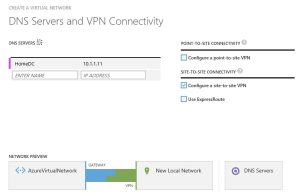
On the next window you can enter the DNS servers. Provide the local DNS server from your internal network and also add the first .4 address of your Azure network subnet. In this case, it will be 10.1.2.4. This as my network is 10.1.2.0/24. Also check the Configure a Site-to-Site VPN box.
On the next page, details for the local site are requested. You can add a name for the gatway (HomeGW), the external IP address and the address space for the internal network. In our case 10.1.1.0/24
On the next page the Azure network specifications must be provided. Note that we added an address space, then a subnet (/27) and a Gateway. This divides our internal usable subnet in small chunks already. So our 10.1.2.0/24 network is now sliced down to an 10.1.2.0/27 network with only 32 addresses. As I will not create that many machines no problem for me. But it may be for you and you want to add additional subnets.
After the network wizard has been completed and the network is created, its time to activate the Gateway.
On the bottom of the page, select DYNAMIC routing
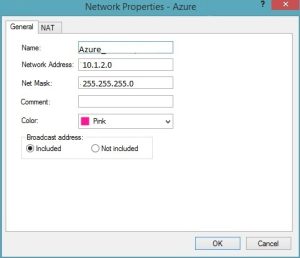
Now while the gateway is creating, its time to prepare the CheckPoint Firewall. First we need to create a network object to represent the networks in Azure.
Next its time to create the Azure Gateway Object in CheckPoint
In this case, the IP address needs to come from the Azure page, after the gateway is created. On the topology tab, select the network “Manually Defined” Azure
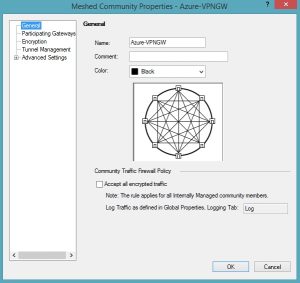
After that we can go to the NAT tab of the SmartDashboard and create a new Mashed VPN setup
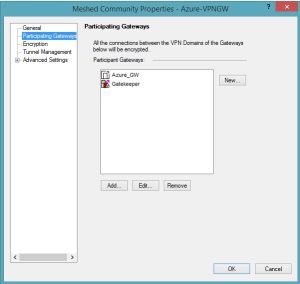
On the participating gateways list, add the local Checkpoint and the Azure object created earlier
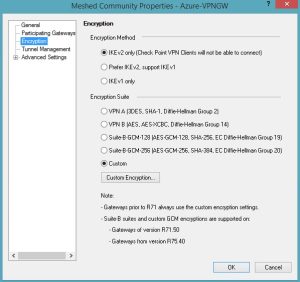
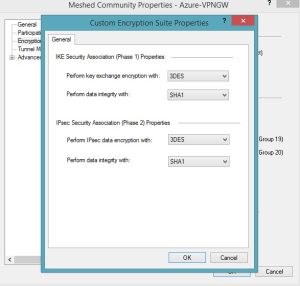
On the encryption tab select:
- Encryption Method
- IKE v2 Only
- Encryption Suite: Custom
- 3DES SHA1
- 3DES SHA1
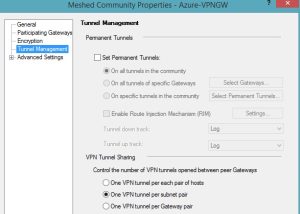
Go to Tunnel Management, and select a single tunnel per subnet
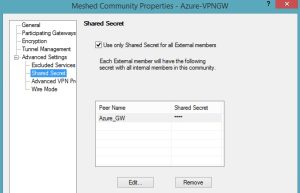
Next the shared secret needs to be filled in, this Shared Secret can be obtained from the Azure portal (Networks). On the bottom of the page of the just created network, select Manage Key
From the pop-up window, copy the key and paste it into the shared key window of the Checkpoint software. Also enable Use only Shared Secret for all External Members
Click ok. Finally the Firewall rules will need to be created. Create 2 rules, one is for the Gateways to actually connect. Using IKE. The second one is to connect the local network to the Azure network.
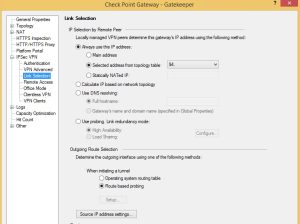
Finally, on the Azure webpage, click CONNECT…. and the connection should be made. If that is not the case, open the properties of the CheckPoint firewall object, go to IPSec VPN and select Link Selection. From that window, select Always use this IP address and select your external IP address.