I know that many of my posts are about networking icw a Juniper SRX… as I happen to have one. But what if you don’t have such a “sophisticated” device that can handle multiple virtual routers, BGP and all the other stuff. Well I could say, buy one from e-bay.. but let’s see if I can help you out to connect to your tenants natively through Windows.
In Windows Server 2012 R2 and above, there is native capability of using S2S VPN services through routing and remote access. Luckily for us, the Azure Stack Host is a Windows Server 2016 server. And the BGPNAT01 is also a Windows Server 2016 server. So, we can actually use those to help us out. (again, please be aware that this is an unsupported action).
Route mode or NAT mode
The trick mentioned in this post works if the BGPNAT is in route mode or NAT mode. But if you want to bypass, and not use the BGPNAT as the VPN endpoint, you need to set it to route mode. The Windows PowerShell instruction given in this post works on all Windows Server 2012 R2 and Windows Server 2016 installations, and thus you could decide to terminate the vpn somewhere else. In that case, in order for your server to be able to make a L3 connection to the VPN endpoint, you need to set it to route mode.. (or add NAT translations to the BGPNAT01). While I think putting it in Route mode is easier, I believe the supported way is to add the NAT translations.
Target selection
There are two targets we can choose. The first being the host itself. This configuration allows the Azure Stack Host to connect to the virtual network deployed in a subscription but given the Azure Stack Host does not route external to internal connections, the connection is isolated from within the host only.
The other obvious choice is the BGPNAT01 VM. This as the VM is already set to RoutingMode (but it seems this also works if it is still in NAT mode) and therefore can also include the routes towards our subscription based network. So, in this example I’m using the BGPNAT01 to achieve the VPN.
How to
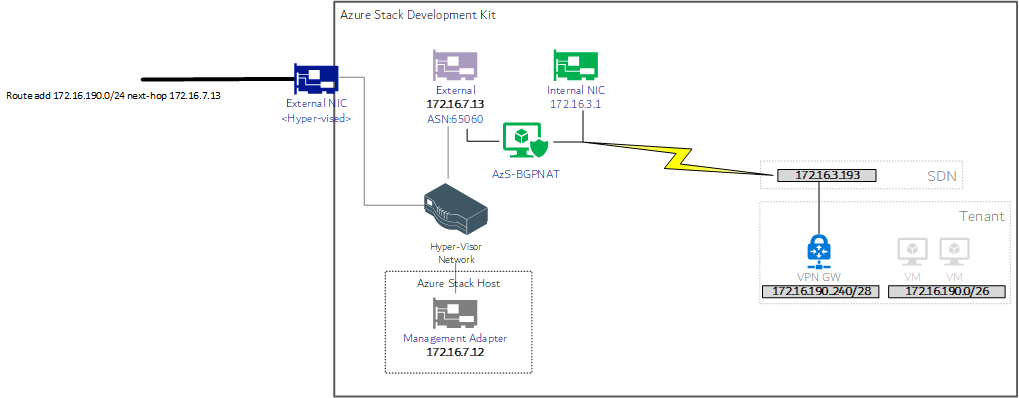
We start by creating a VNET in a subscription inside the Azure Stack Dev Kit. I set the address range to be 172.16.190.0/24. The default subnet is set to 172.16.190.0/26. Then I created a new GatewaySubnet at 172.16.190.240/28 and deployed a Virtual Network Gateway.
Now in my setup I actually changed the addresses a bit, so please bear with me and replace all the 172.16.3.xx addresses to 192.168.200.xx if you did a default deployment.
My “external IP address” for the GW was set to 172.16.3.193 (yours is probably 192.168.102.x)
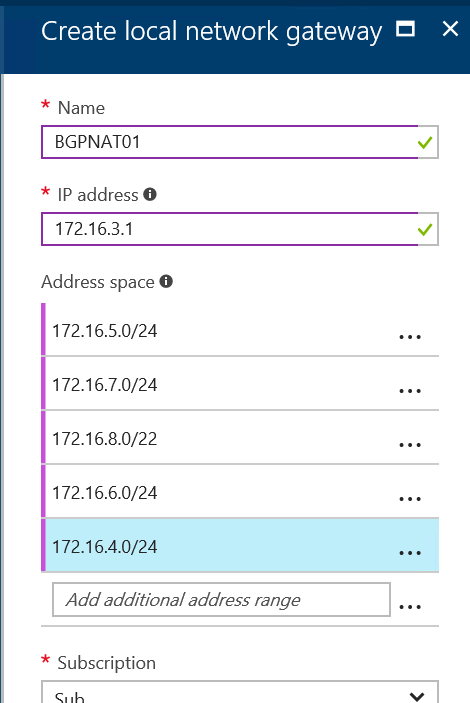
Next is the creation of the Local Network Gateway. In here we define the endpoint IP address (which needs to be the 172.16.3.97 (in yours probably 192.168.200.65), the Pre-SharedKey (12345) and the subnets that are behind that VPN endpoint (in my case 172.16.5.0 (internal), 172.16.7.0 (stack), and some more..)
Side note: if you BGPNAT01 is in route mode, your endpoint IP address can also be the “outside” interface of the BGPNAT01.
And that is all you have to do from the Subscription side.
Next is the BGPNAT01 router.
On the Azure Stack Host, open a notepad and paste the following lines of code
Add-VpnS2SInterface -Name Test2 -Protocol IKEv2 -Destination 172.16.3.193 -AuthenticationMethod PSKOnly -SharedSecret '12345' -Persistent -IPv4Subnet 172.16.190.0/24:100 -DHGroup Group2 -AuthenticationTransformConstants GCMAES256 -CipherTransformConstants GCMAES256 -EncryptionMethod AES256 -PfsGroup PFS2048 -SALifeTimeSeconds 14400 -SaRenegotiationDataSizeKB 819200 -MMSALifeTimeSeconds 28800 -CustomPolicy
[edit: Quick mode SA Lifetime (in seconds) is actually 14,400 seconds, not 3600 – it was a mistake in the original docs from MS]
In the command in notepad, change the -Destination 172.16.3.193 to the “external IP” of your deployed Virtual Network Gateway. Change the IPv4 subnet -IPv4Subnet 172.16.190.0/24:100 to match your deployed Virtual Network address space in the subscription. Make sure to add :100 to the /24 to avoid getting an error.
Copy the entire piece of text (make sure to check “” and ” if they are ok…) then logon to the AzS-BGPNAT01 and type PowerShell to get into the powershell command mode. next, paste the piece of text and execute (hyper-v paste will work)
If all is well, the connection should come online in a few seconds

Which you can check with the Get-VPNS2SInterface command.
Don’t be alarmed if you cannot ping the internal subnet from the BGPNAT machine, you will be able to ping it later when you added the route to your external networks.
On the Azure Stack Dev Kit host, open a command prompt (in admin mode) and add the route to test:
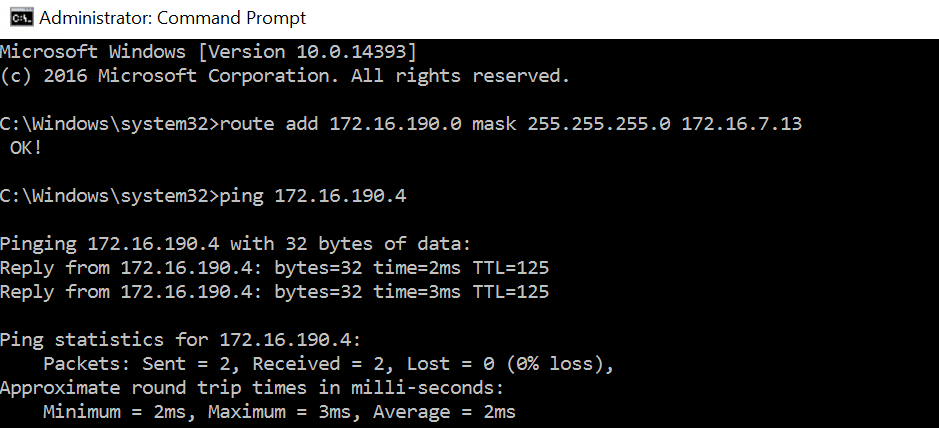
Now, given the BGP advertisement (see other post) does not include the S2S remote VPN address tables, we need to manually enable this on the core router (yes, here is the Juniper again). But after pointing my 172.16.190.0/24 next-hop BGPNAT01, I get the following:
(EDIT: by adding the 172.16.190.0/24 subnet in the BGP advertisement, I dont have to change anything and the BGPNAT will automatically update my Juniper: add-BGPCustomRoute 172.16.190.0/24)
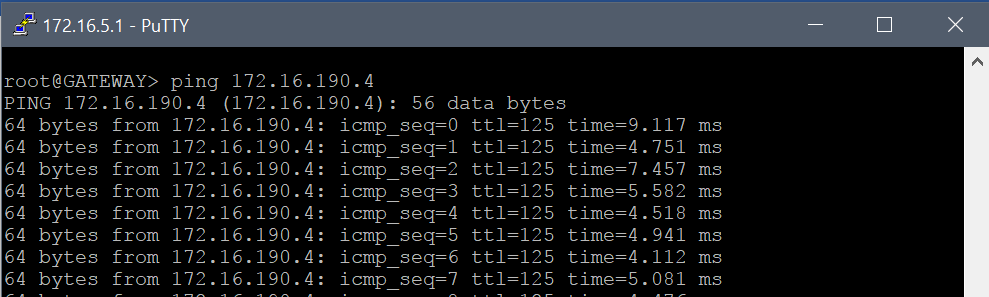
And that’s it.. the VPN is indeed active on the BGPNAT01 (in route or NAT mode) and I can forward the traffic on my internal network to the BGPNAT01 (which has an external IP address – in the same range as the Azure Stack Dev Kit host). And that means… even without an expensive router, I can still make S2S VPN connections to my subscription networks.